Back to Forensic Science
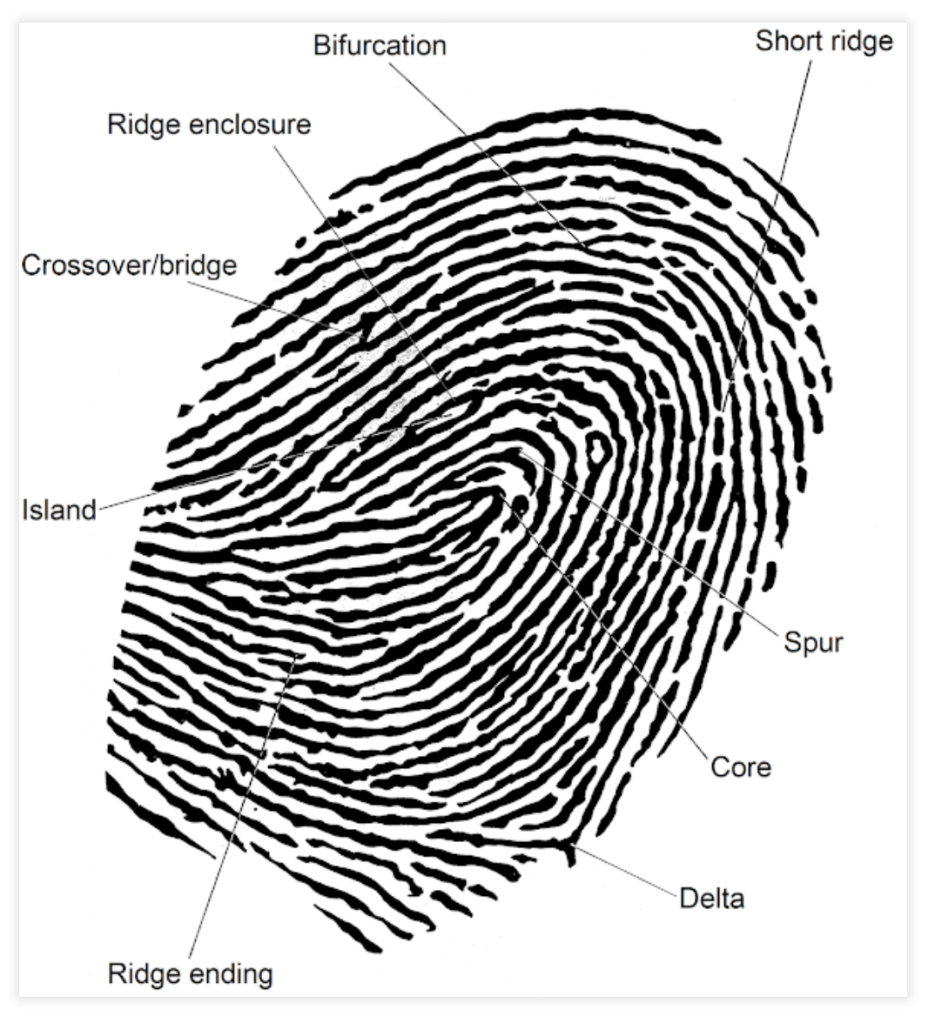
Fingerprint analysis uses the location, direction,
and type of minutiae points to match fingerprints.

Fingerprint Patterns
- There are a handful of different fingerprint patterns, for example:
- Top Row, Left to Right
- Loop, Double Loop, Central Pocket Loop
- Bottom Row, Left to Right
- Plain Whorl, Plain Arch, Tented Arch.
- Top Row, Left to Right
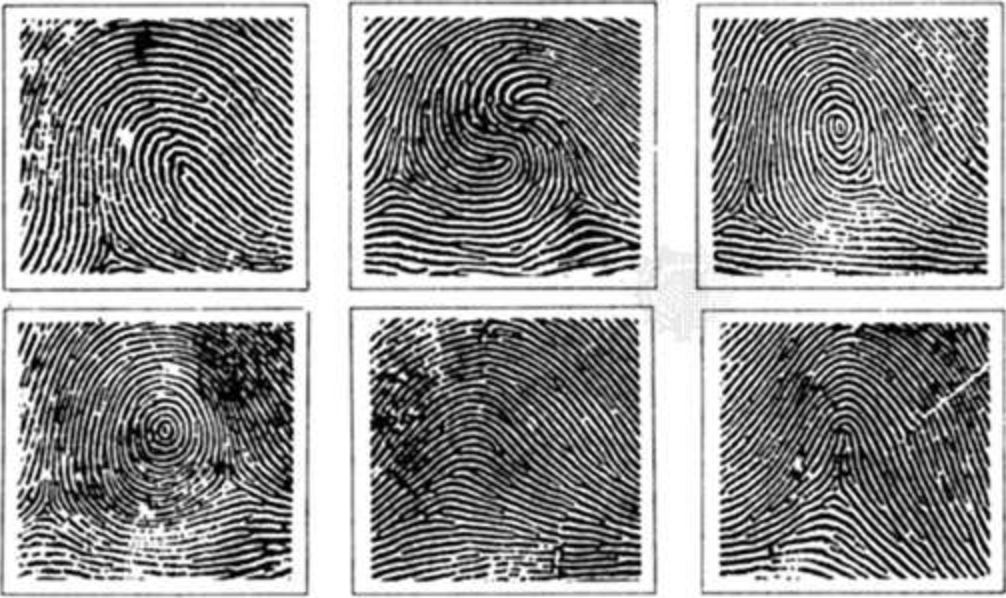
- If fingerprints (of the same finger) have different patterns, they are obviously from different people.
- A more granular method is needed for matching fingerprints.
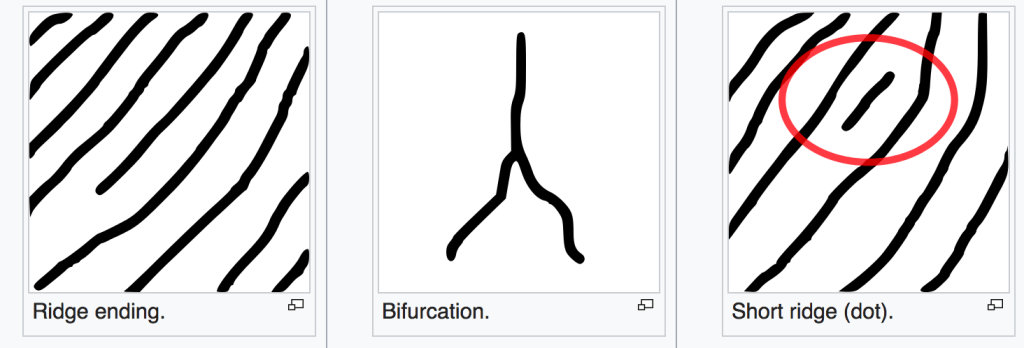
Minutiae-based Matching
Minutiae-based matching uses the location and direction of minutiae points.
From Syahrul’s Block
- Ridge ending – the abrupt end of a ridge
- Island – a single small ridge inside a short ridge or ridge ending that is not connected to all other ridges
- Crossover or bridge – a short ridge that runs between two parallel ridges
- Ridge enclosure – a single ridge that bifurcates and reunites shortly afterward to continue as a single ridge
- Ridge bifurcation – a single ridge that divides into two ridges
- Short ridge, or independent ridge – a ridge that commences, travels a short distance and then ends
- Spur – a bifurcation with a short ridge branching off a longer ridge
- Core – a U-turn in the ridge pattern
- Delta – a Y-shaped ridge meeting
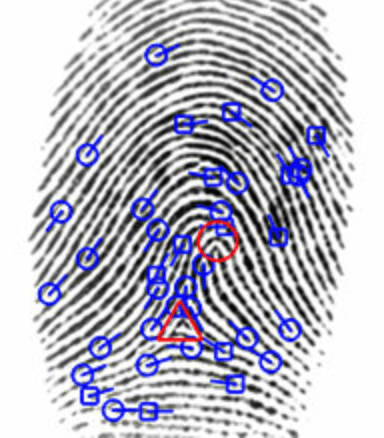
Automated Fingerprint Identification Systems
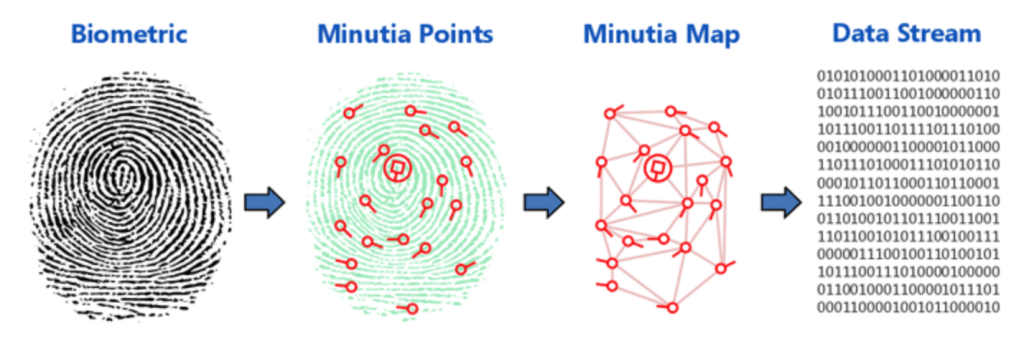
Image Credit identityone.net/BiometricTechnology.aspx
- britannica.com/topic/dactyloscopy
- “In the 1980s the Japanese National Police Agency established the first practical system for matching prints electronically.
- Today police in most countries use such systems, called automated fingerprint identification systems (AFIS), to search rapidly through millions of digitized fingerprint records.”
- Integrated Automated Fingerprint Identification System (IAFIS)
- “Maintained by the FBI Criminal Justice Information Services (CJIS), IAFIS contains over 47 million subjects. System capabilities include automated tenprint and latent fingerprint searches, electronic image storage, and electronic exchanges of fingerprints and responses.”
- wikipedia.org/wiki/Integrated_Automated_Fingerprint_Identification_System
- “IAFIS houses the fingerprints and criminal histories of 70 million subjects in the criminal master file, 31 million civil fingerprints, and fingerprints from 73,000 known and suspected terrorists processed by the U.S. or by international law enforcement agencies.”
Latent Fingerprint Analysis
From PCAST Report
- Foundational Validity
- “Based largely on two recent appropriately designed black-box studies, PCAST finds that latent fingerprint analysis is a foundationally valid subject methodology — albeit with a false positive rate that is substantial and is likely to be higher than expected by many jurors based on longstanding claims about the infallibility of fingerprint analysis.
- Only two properly designed studies of the reliability of fingerprint have been conducted. One study found that the false positive rate was 1 out of 306. The other found that the rate was 1 out of 18.”
- Validity as Applied
- “Confirmation Bias. Work by FBI scientists has shown that examiners typically alter the features that they initially mark in a latent print based on comparison with an apparently matching exemplar. Such circular reasoning introduces a serious risk of confirmation bias. Examiners should be required to complete and document their analysis of a latent fingerprint before looking at any known fingerprint and should separately document any additional data used during their comparison and evaluation.”
- “In 2005, an international committee established by the FBI released a report concerning flaws in the FBI’s practices for fingerprint identification that had led to a prominent misidentification. Based almost entirely on a latent fingerprint recovered from the 2004 bombing of the Madrid commuter train system, the FBI erroneously detained an American in Portland, Oregon and held him for two weeks as a material witness. An FBI examiner concluded the fingerprints matched with “100 percent certainty,” although Spanish authorities were unable to confirm the match. The review committee concluded that the FBI’s misidentification had occurred primarily as a result of “confirmation bias”.”
View PCAST Report